Over the past year, we have witnessed an increase in the number of phishing campaigns in Lebanon and amongst the Lebanese diaspora. Most users have received phishing links through WhatsApp and email; almost all of these campaigns rely on human error, so users need to take precautions to protect themselves. The list below may help you avoid phishing links, but it is not exhaustive
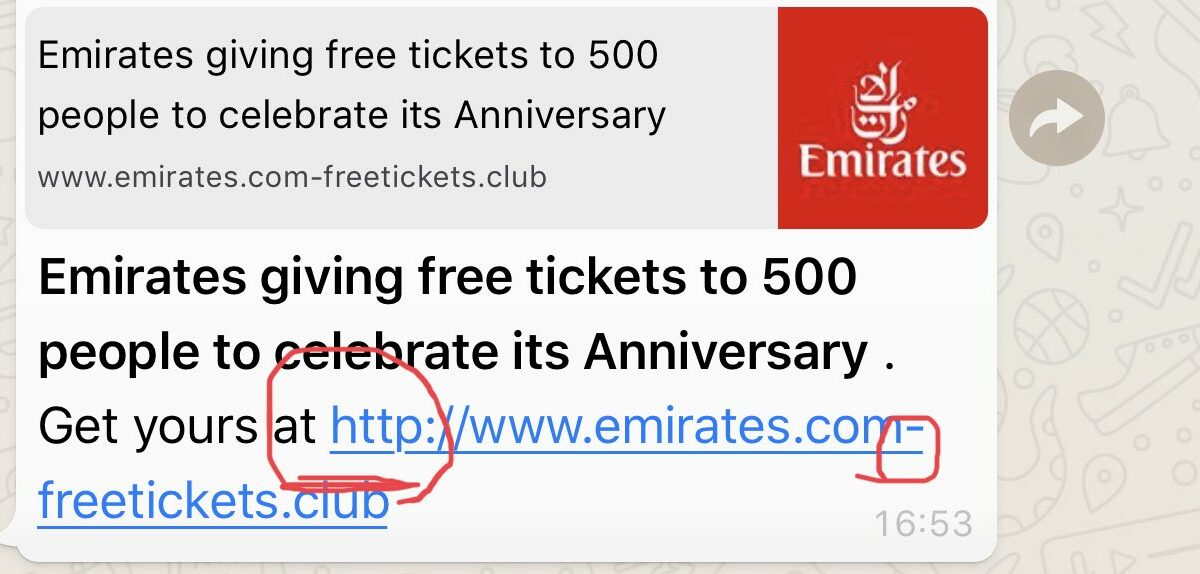
- Phishing links are usually malformed; they try hiding by exploiting your attention. For example, instead of http://google[.]com, a phishing link might read http://googl[.]com. Stay away from these links.
- If a link is presented in a shortened form like bit.ly, goo.gl or another format, this might be for a few reasons:
- The link is long, and the sender wishes to shorten it.
- The sender of the link wants to redirect traffic from another website to improve Search Engine Optimization (SEO).
- The sender is hiding something that is potentially dangerous.
- The link is long, and the sender wishes to shorten it.
You should always check shortened URLs. The best way to check them is to use a URL unshortener. If the URL unshortener does not verify the link, recipients should not click on it.
- If you receive an email containing a link, you can see where it will redirect you to by hovering the mouse over the link, which might reveal either an IP address or a web address for example in a little yellow or white box .This technique can help you detect a malicious link.
- Known entities, such as Google, Microsoft, or other large companies, always address the recipient by name when they send emails. If your name is not shown correctly in the email, this is likely a phishing email.
- Phishing messages also try to inspire fear or excitement. For example, a phishing message may read “if you don’t click this link your email will be deactivated”, or “free gifts.” If these messages are unexpected, they are likely phishing messages.
- Check the “From” and “To” fields of the email. If the email is not addressed to your email directly, something is “phishy.” If the email source seems legitimate, the sender could have still used hiding techniques in the email headers, as there are plenty of issues in mail servers.
- Legitimate entities use common known TLDs (Top-Level-Domains). Domains like .club, .tech, .win, etc. are likely fake pages. For example Emirates Airlines will not send you a link with a .club link! They have a well-functioning .com domain name and they care deeply about their SEO. They will not redirect you to a bizarre TLD.if you are not 100% certain about the real domain, you should search it on Google, Bing, DuckDuckGo, or another search engine.
- Complex domain names with many dashes, numbers, and dots are likely fake links. Therefore, the links could be part of a phishing campaign. For example, http://freeticket-xn--8973.smexclub[.]win is likely a phishing link.
- Words like “URGENT,” “GREETING,” or other words that denote immediate action are often used in phishing scams. For example, if you did nothing on the Apple website in the last 24 hours and you are not expecting a message from the company, it is unlikely that it is actually sending you an email with “URGENT” in the subject line. Be wary of messages with these words in the subject line.
- The vast majority of big companies have adopted https. If you don’t see a lock on your browser URL field, don’t proceed. In Firefox, the lock should be green and in Google Chrome, you should click on the lock and it should read encryption secure in green letters.
- The pages phishing links redirect you to often request personal information. For example, these pages might request your name, phone, and/or email. Even if the web pages are not collecting passwords, collecting other personal information is a fundamental part of the reconnaissance phase of a staged hacking campaign. Never input your personal information on a website you do not trust.
If you have any questions or tips about phishing campaigns you have been exposed to, please send an email to Ragheb[at]smex.org