An exploit in touch’s SIM Application Toolkit (SAT) protocol enables companies and individuals to access any touch SIM card and send messages without the owner of the SIM card’s knowledge, a source familiar with the situation told SMEX. According to the source, touch SIM cards have been vulnerable for at least the past five years and the millions of people who currently have touch SIM cards are exposed to this threat.
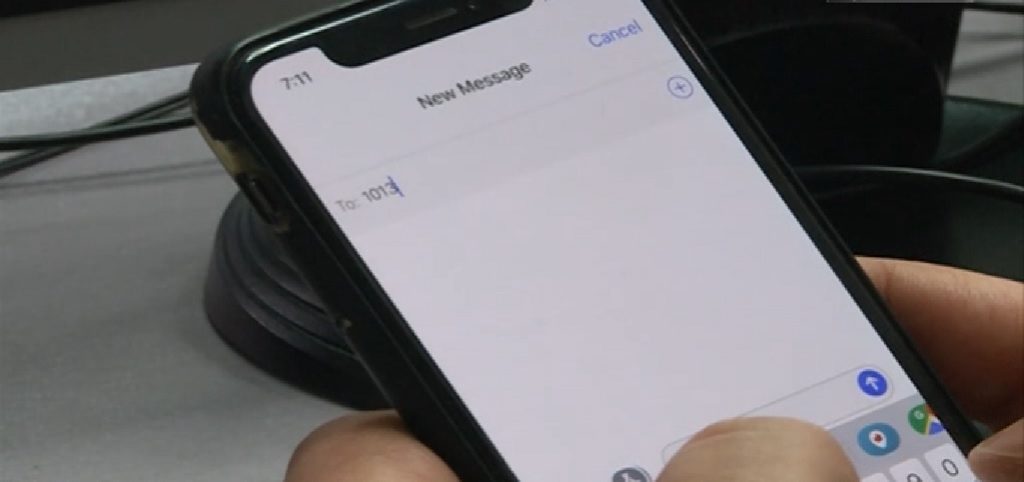
The source contacted SMEX after a report by Adam Chemseddine at Al-Jadeed revealed that touch, one of the two state-owned operators in Lebanon, allowed COMEX, a bulk messaging service, to exploit the vulnerability in touch’s SAT protocol and steal money from customers. In 2017, touch customers began reporting that they erroneously received a $.90 surcharge for sending SMS messages to numbers 1084 and 1013, despite the fact that these messages did not exist in their phone. These numbers, operated by content provider COMEX, sent a binary code to a number of SIM cards that triggered each SIM to send a message containing either a “9” or an “11” in return to 1084 or 1013.
By sending the message, customers incurred a $.90 charge, which netted COMEX over $17,000. In touch’s internal report about the incident, the company found the four digit numbers generated a far larger number of Mobile Originated (MO) messages than Mobile Terminated (MT) messages, which are triggered by MO messages. If the campaign had managed to generate an equal amount of MT messages, COMEX would have managed to steal almost $99,000 from touch customers, according to the report.
As SMEX recently learned, any actor can take advantage of this same exploit in touch’s SAT protocol to perpetuate similar schemes. Essentially, any individual or company with the ability to manipulate the binary code can send messages from any device with a touch SIM card, without the owner knowing the message has been sent. Therefore, not only are bulk messaging services, like COMEX, able to take advantage of this weakness, but any individual could generate a fake text from a phone with a touch SIM card.
The revelation that touch’s SAT protocol is outdated and vulnerable further highlights touch’s disregard for its customers and consumer protection in general, In the Al-Jadeed report, SMEX executive director Mohamad Najem stressed that “InfoSec experts with advanced technical skills should be recruited by Alfa and touch to better detect such vulnerabilities.” With the news that the vulnerability is much larger than initially anticipated, touch should take immediate measures to protect its customers’ privacy.
SMEX recommends that touch:
- Either push an update on existing SIM cards or issue new SIM cards to fix this vulnerability and protect customers’ data from third parties.
- Opens an investigation on COMEX to identify if this is still happening and make sure that investigation includes any other third party that used COMEX’s license
- Conducts an audit to see if this same practice has happened or is currently happening with other 4 digits servers.
SMEX recommends that parliament:
- Update the E-Transactions and Data Protection Law to offer better protection for personal data.
- Enact stronger consumer protection laws, particularly concerning mobile operators, to ensure that people’s communications devices are protected.
SMEX tried to reach out to touch for a response, but the company requested that we send a formal written letter to their Public Prosecution team. We sent the letter and await the company’s response.
(Original photo is a Screenshot from al-Jadeed report)
Watch the full report here.