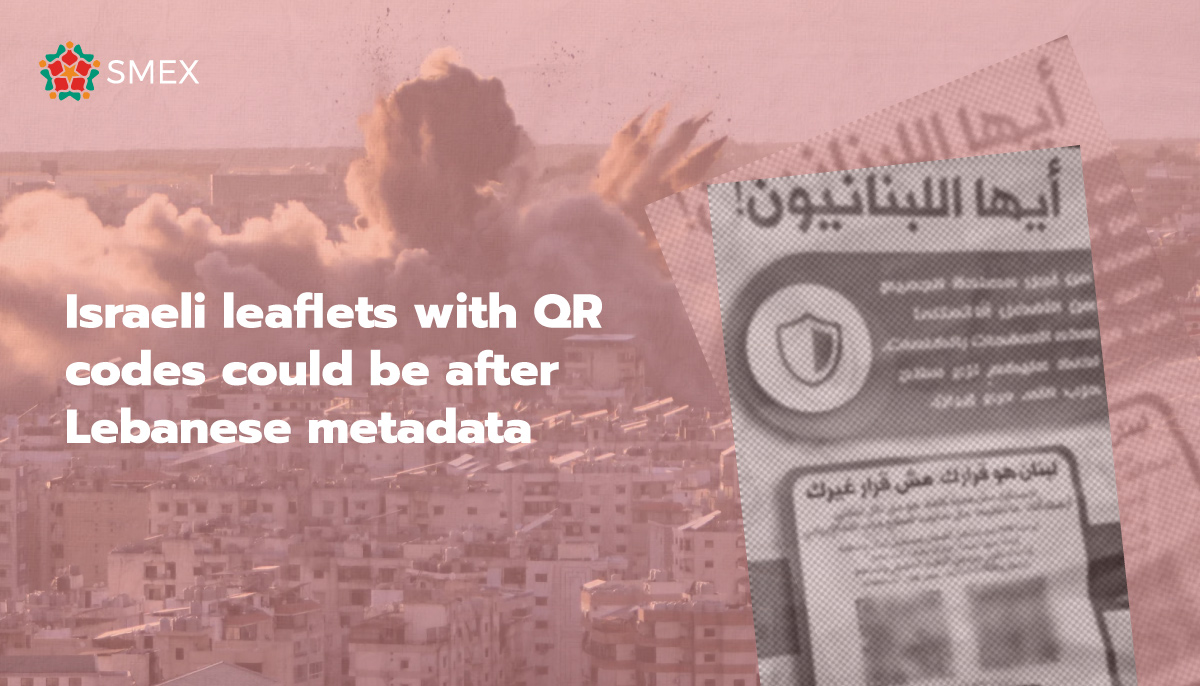
On March 13, thousands of leaflets dropped over Beirut. At the bottom sat QR codes A month later, the question remains: why would a military drop QR codes for people to scan? Were they malicious? And what were they actually trying to collect?
I believe they were after metadata.
Metadata is generally defined as “data about data” — the extra information attached to a file or action online, that allows it to travel correctly from one place to another over the internet. Think of it like sending a package: the photo is the item inside the box, that is your data. The label on the outside is the metadata: it tells us the location where it was shot, the date it was taken, its file size, and the phone type for example. The label tells the system where the package is going, where it came from, and what is inside. Without it nothing arrives.
The label, or the metadata is not encrypted, since the system needs to read it to know how to direct it.
Most metadata falls into three categories:
- Descriptive metadata identifies and locates the data, for example, where a photo was taken, where a QR code was scanned, or which city a website was accessed from.
- Administrative metadata covers how data is managed. This includes device information: your IP address, your device type, your operating system, your browser, and the time you accessed a site. This is the data a website uses to load correctly on your device, run security checks and track how it is being used.
- Structural metadata shows how data is put together. It defines how content is organized, structured and linked so it can be displayed correctly on your screen.
Metadata is a condition for performing any kind of digital activity. Every time you open a website, log onto social media, or take a photo, it is produced automatically, as a function of how digital systems work.
So, how does metadata connect to the flyers that fell over Beirut sky a month ago?
Because metadata is unencrypted and produced automatically, it can be collected by anyone running the service you are connecting to, legally and routinely.
The moment someone in Beirut scanned the QR code and got redirected to the Mossad’s Facebook page through the flyers, the collection began. Though the QR codes may have led to WhatsApp or Facebook, users could have first been redirected through intermediary pages equipped with digital tools that can collect data before they passed them on.
By the time they reached what the final page is, their IP address, location, information about their device, the time they accessed the website. Could have all been collected. This is not malware and is collected by any website offering a functional service. The difference is who is collecting it and what they intend to do with it.
In a wartime context, the flyers dropped over a city could be used to collect important information about users. Location, time, device, and network can establish where a person is at a given moment.
Mass surveillance does not necessarily require sophisticated spyware. Sometimes it is about taking advantage of what can be done legally and using it to weaponize normal day to day activities.