Image via Citizen Lab March 9, 2018: Adiagram explaining how the DPI middlebox worked in Egypt.
The discovery of the Dark Caracal surveillance scheme in Lebanon earlier this year put the world on notice that states in the MENA region are developing significant digital surveillance and information control capacities of their own. Now new exploits in Turkey and Egypt have been revealed.
According to “Bad Traffic,” a new report from the University of Toronto’s Citizen Lab, unknown operators in both countries have been redirecting users without their knowledge to web pages they did not request.
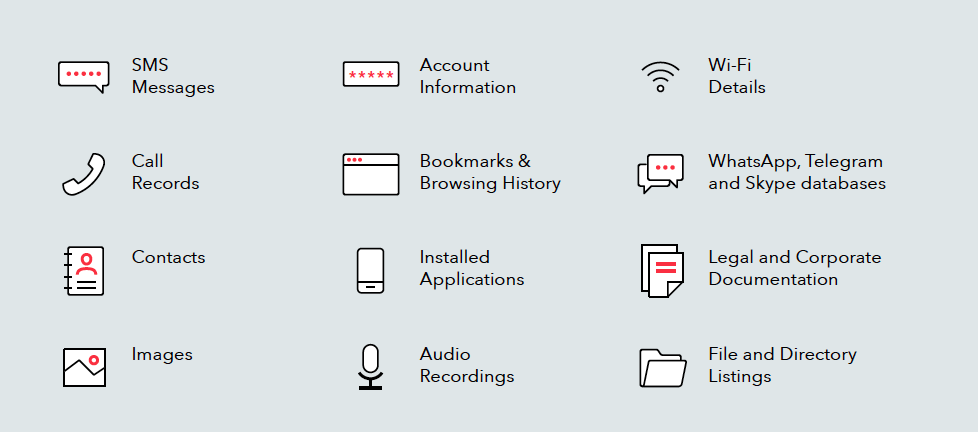
The exploits made use of deep packet inspection (DPI) middleboxes, black boxes that sit between a user and the server they are trying to reach and alter the traffic passing through them by injecting code that can redirect requests to another, unwanted destination over an insecure connection.
In Turkey, the middleboxes, which Citizen Lab identified as SandVine PacketLogic devices, redirected Türk Telekom users in five provinces and parts of Syria who were “attempting to download legitimate programs to versions of those programs bundled with spyware.”
Further analysis revealed that the operators of the middleboxes were connected to other exploits that included the use of FinFisher, a surveillanceware that targets computers and is sold exclusively to law enforcement agencies, most likely implicating the Turkish government as the actor behind this operation.
In Egypt, users of Telecom Egypt were redirected to a mix of websites filled with advertisements and cryptocurrency mining sites, in an exploit researchers dubbed “Adhose.”
Researchers could not rule out the Egyptian government’s involvement in the operation, but Amr Gharbaya, the civil liberties director at the Egypt Initiative for Personal Rights, posited that it could also be a covert initiative by a private engineer trying to make some money.
While Sandvine, a Canadian company owned by the U.S private equity firm Francisco Partners, denounced the findings of the report, Citizen Lab found LinkedIn profiles of SandVine employees currently working in both Turkey and Egypt.