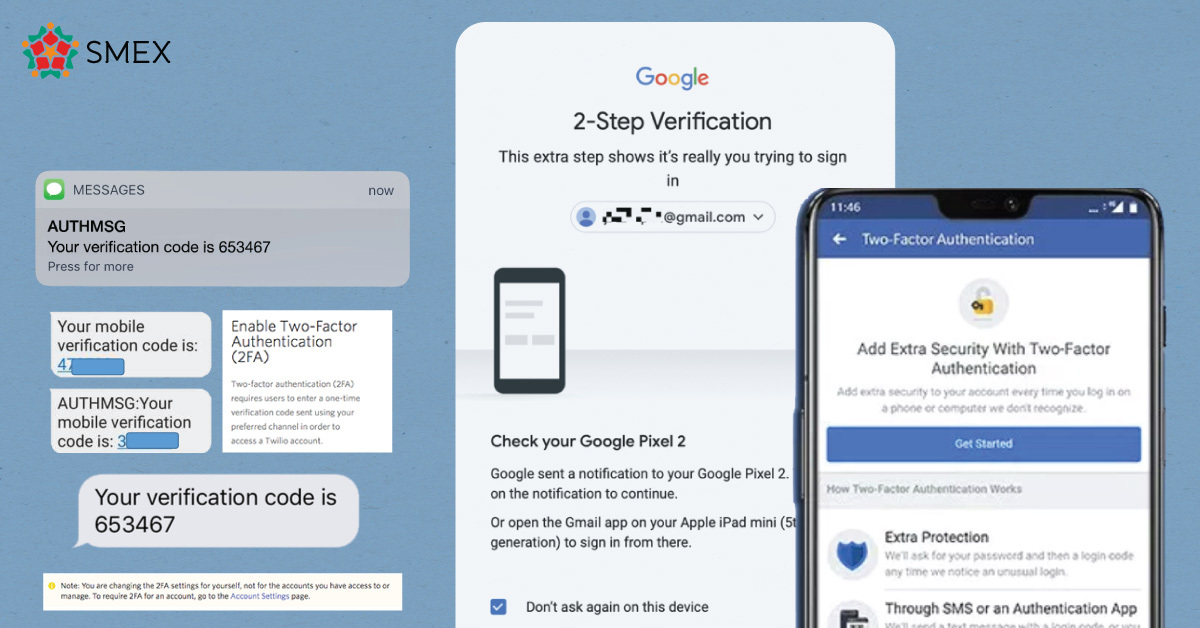
Our team has been receiving a significant number of SMS messages from a source identified as “AUTHMSG.” This sender name is used by many apps that use the Two Factor authentication service. More and more people are reporting that they’re receiving similar messages. This is a legitimate concern; and here’s why.
What in the SMS is AUTHMSG?
The name “AUTHMSG” isn’t bizarre or new. Twilio, a communication tools provider, announced this service for sending text messages through APIs.
“As part of our ongoing improvements to these APIs, we are announcing the introduction of AUTHMSG, an Alphanumeric Sender ID, for use in 79 countries, which will further increase conversion. If you are already a customer of these APIs, this change will be made automatically.”
All details can be found on https://www.twilio.com/blog/authmsg.
Twilio is providing Alphanumeric sender IDs which can be customized by clients in order to show the sender’s business name rather than an anonymous number, i.e. “YourPreferredOnlineStore” instead of “+961 xx xxx xxx.”
So what’s the problem?
In this context, AUTHMSG is used to refer to the sender of a two-factor authentication (2FA) code, like Signal, Whatsapp, or any other service.
Basically, a lot of service providers might refer to Twilio Authy services which are represented by AUTHMSG, and these local carriers have registered a set of phone numbers as AUTHMSG. It might appear that you are constantly receiving messages from the same source, which might not be the case. The problem is that all the services using Twilio Text Messages as a third-party for sending SMS in case of 2FA or activation might end up showing at the same place in your text messages inbox, under AUTHMSG.
So whenever you or someone else try to reset your 2FA verification code, you will receive a message from AUTHMSG.
These messages can be safely ignored if you did not attempt to log into an account, and as long as you have strong passwords and other digital security measures.
Why am I receiving a ton of messages from “AUTHMSG”?
The texts you are receiving from AUTHMSG are usually, but not necessarily, received after an attempted login takes place without the proper credentials (recovery method), or from an unknown device, which triggers your third-party verification service to text the account in question.
So you are not a direct target of these login attempts, but it’s probably a wide-scale spam attempt that broadcasts these messages to a set of phone numbers/accounts on the service from which you are receiving these constant repetitive messages.
Unless your GSM provider is getting hacked, and the verification SMS texts are being intercepted, there’s nothing to worry about. The fact that you are receiving a lot of these messages also means it’s probably an untargeted attack.
So why are the attackers doing this?
It could be a form of infrastructure fatigue, to check how the services would function if the SMS verification goes down. Since it is a large-scale spamming campaign, it could also mean that the malicious actors are playing a game of guessing as well, trying until it crashes or functions.
Recommendations
- Ignore the messages from AUTHMSG unless you have just made a request for a verification code
- Do not send these codes to anyone, ever.
- Change your password frequently every month or a few months
- Generate and use strong passwords using an encrypted Password Manager like Bitwarden
- Activate the two-factor authentication process and make sure it is activated on all your accounts, especially the ones that you are receiving codes on
- Clean up your account from all third-party access
- Adapt and use Multi-Factor Authentication (MFA ) instead of two-factor authentication (2FA)